Application Preview
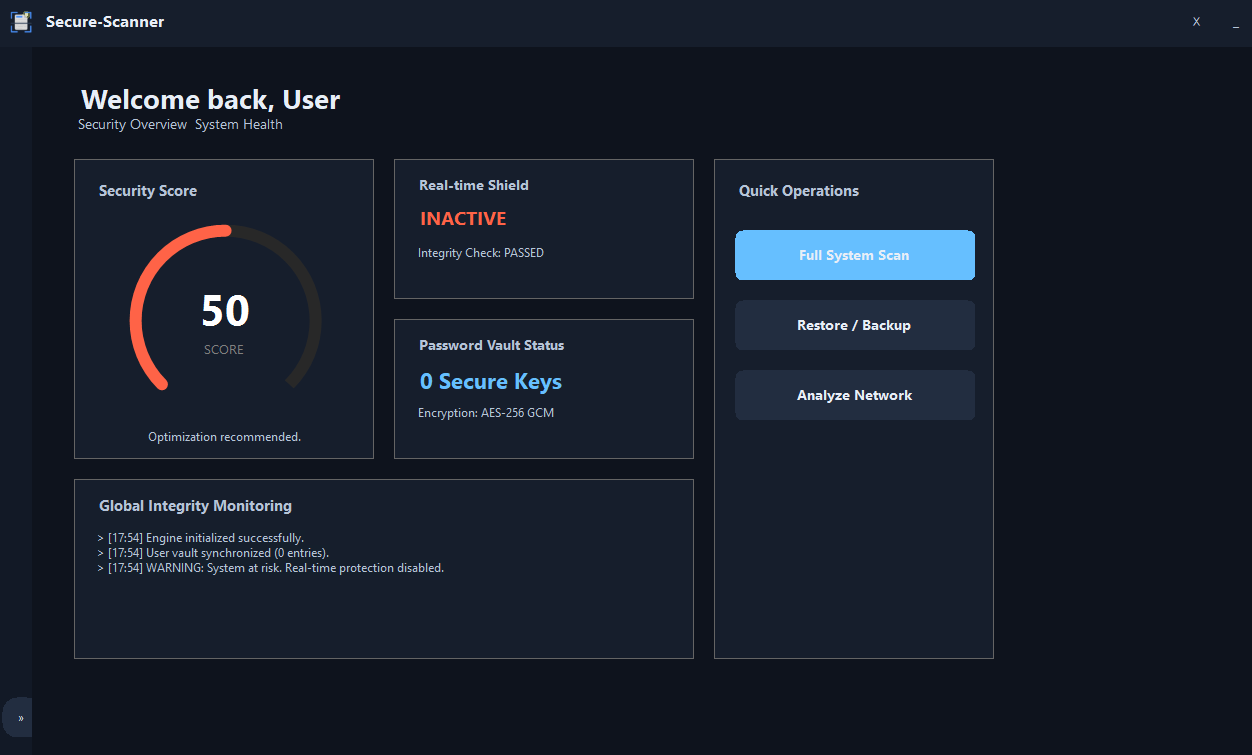
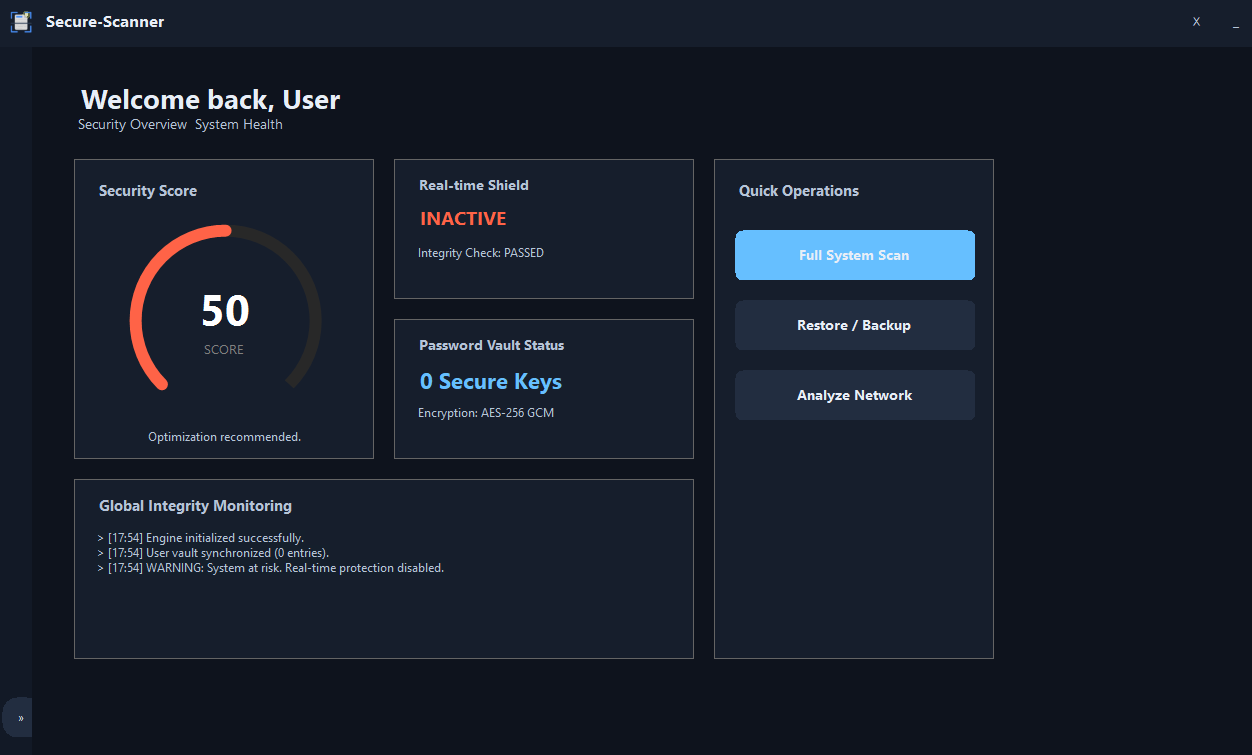
Detect threats based on behavior, not just signatures.
Continuously monitors your system activity.
Protect credentials with encrypted storage.
Analyze suspicious connections in real time.
Run unknown files safely in isolated environments.
Track all scans and detected threats easily.